Encryption keys
One of the key features of UNLOQ is providing and delivering personal encryption keys that can be used to store sensitive information in its encrypted form and only decrypt it when a user explicitly requires it. The encryption key is generated on the user's device and is cryptographically safe, using native modules to generate random bytes.
The personal encryption key is generated for each UNLOQ account - application combination the first time it is requested. Once the device has generated the key, a second generated encryption key is used to store it encrypted on the user's device. The second key divided into three sub-components, two of them stored in two different geographical regions and providers, and the third component is dynamically generated based on a derivation of the user's PIN
Even in the event of the user deactivating his account and re-activating it on a different device, it will be able to re-construct all his personal encryption keys and use them like nothing happened.
You can enable the use of personal encryption key for your application, by navigating to the Encryption menu item, set the key size and then select one of the three ways to work with encryption keys.
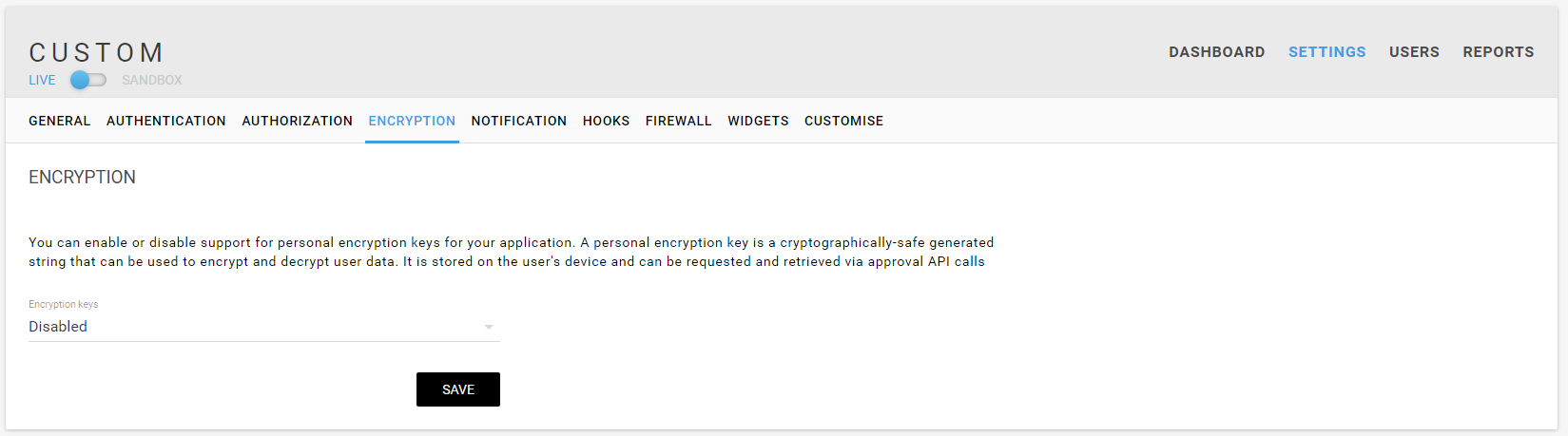
UNLOQ currently offers three ways to use and provide the personal encryption keys:
- Request via widget authentication - The encryption key will be requested every time a user tries to login to your application using a login widget. The encryption key will be provided when your server calls the token fetch endpoint to retrieve the user information. Using this setting will not allow you to request encryption keys via the API call.
- Request via API calls only - The only way to request a user's encryption key is to call the API endpoint and await the user's approval on the request. No encryption key will be provided when a user logs in.
- Always request - This is a combination of the above settings, where the encryption key is requested on each user login to you application and also allows you to ask for the encryption key via API calls.
Note: You can also include a PEM-formatted public key to encrypt the user's encryption key on transit from his device to either your servers or in the browser. This will make sure that it does not pass in plain text through UNLOQ servers, as the public key is transferred directly into the user's device and is used to encrypt the user's personal encryption key on the spot.
Have a question? You can always send us an email at support@unloq.io, or contact us on chat.
For security related concerns, please visit our Security page.