Firewall
In the Firewall section of an UNLOQ application, you can enable some custom rules that will apply to authentications, authorisations or encryption key requests. These allow you to restrict the access of your users in order to prevent undesired approval requests.
Firewall entries are divided into two categories:
- API - These rules will be applied on API calls from your servers. This is useful when you want to enable API calling only from specific IP addresses or ranges
- Approvals - These rules will be applied on user approvals via browser origins and device IP addresses.
With City wall, you can configure your application to only allow authentication requests from a specified list of geographical countries or regions. You can also restrict these requests to a specified IP or range of IP addresses.
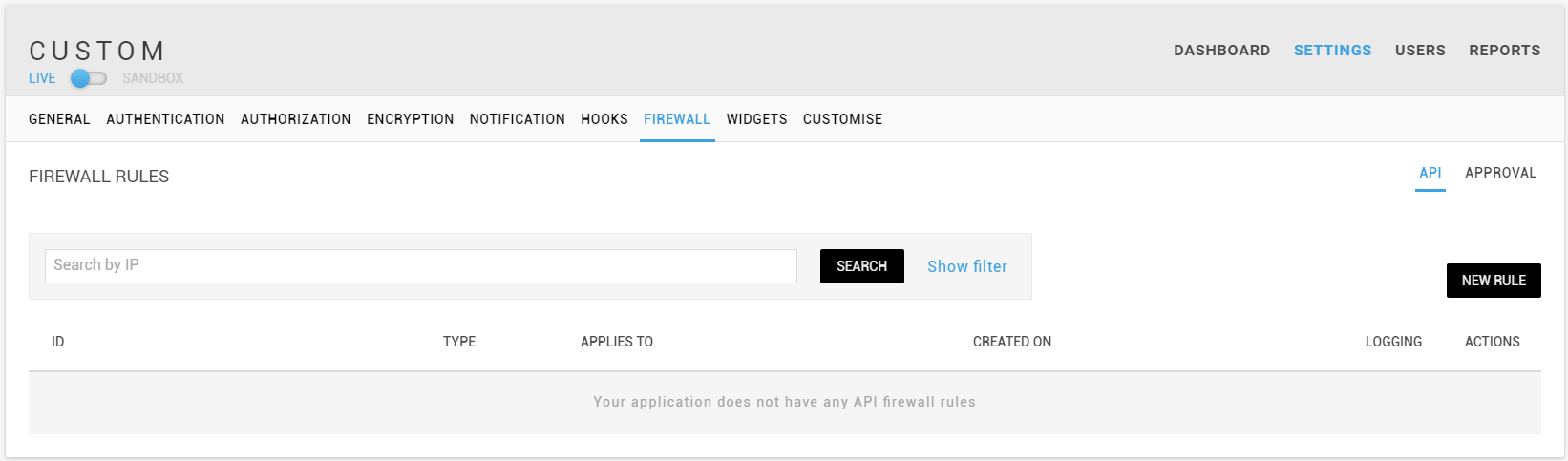
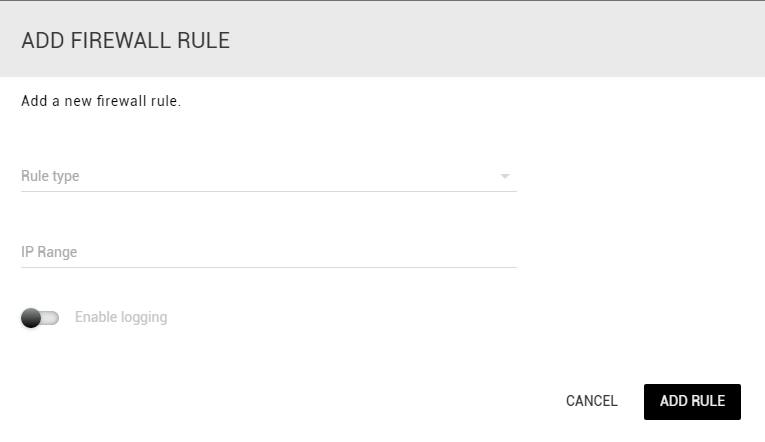
Creating a new firewall entry
You can create a new Firewall entry by clicking the New rule button for either API or Approval. When adding a restriction, you must specify what kind of rule to apply to the selected region or IPs. Selecting Allow will allow any incoming requests, while Block will deny them. When creating a blocking filter, you can also choose to log failed attempts, to later visualize.
By default, the login filters apply on the IP address of the user that initiates the authentication process (the
user's browser). when an authentication push notification reaches the
user's device, it will verify that the device's IP
address matches at least one of the filter's rules (see below).
If the IP address is blocked, or within a restricted geographical region, the authentication process is stopped,
thus forcing the user's device to be in one of the accepted filters.
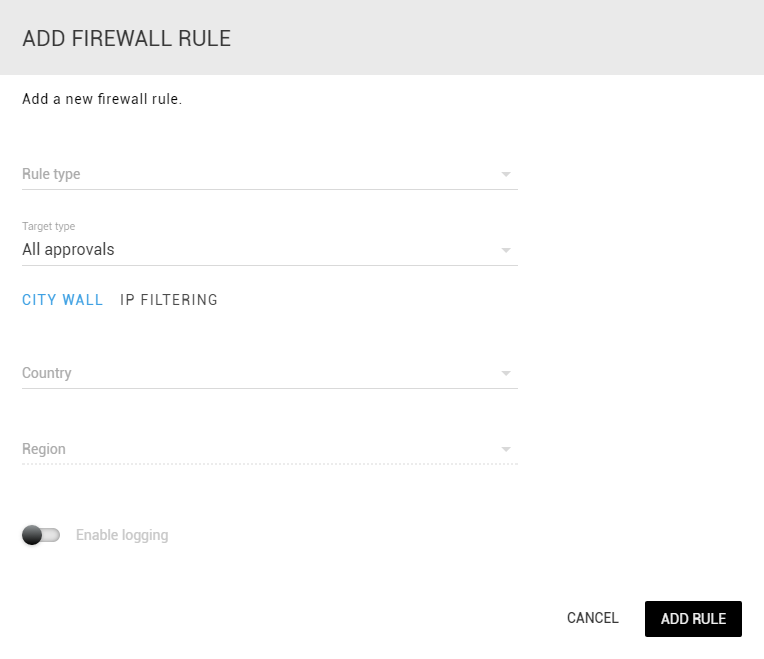
IP restrictions for API calls require just the rule type (Allow/Block) and the IP range to apply the rule to.
Use case: geographical limitation
Let's say we want to enable only users in the UK and Dublin, Ireland to authenticate to our application. We would have to create 3 simple city wall rules:
- Allow all regions from the United Kingdom
- Allow the Dublin region from Ireland
- Block all countries
At this point, any user that will try to authenticate from outside the geographical regions that we've specified,
will be blocked, and their attempt logged.
A user from Clare, Ireland will be blocked, while a user from Birmingham, UK will be allowed.
Note: Geo-location accuracy is between 80-100%, depending on the country.
Use case: IP restrictions
Let's say our company, Acme INC has implemented the UNLOQ authentication system on their applications, and wants only employees that are on-premise to login to their system. In one building, the company has 1 static IP, 2.3.3.3 and the IP range 2.2.2.0 - 2.2.2.244 in another building. The IP restrictions would be as follows:
- Allow IP 2.3.3.3
- Allow IP block 2.2.2.2/24
- Block IP range 0.0.0.0/0 (Don't allow anyone)
With this example, we would block all IP addresses, except the ones that our company uses, therefore, a users will have to use the company's internet connection, in order to login to the application. The same rules can be applied for API calls.
Combining IP filtering with geographical restrictions
Your application can have up to 50 filtering rules of both IP and geo restrictions. These rules are applied as follows:
- Verify that the source IP is allowed (match a static IP or within an IP range)
- Verify if the source IP is blocked (match a blocked static IP or a range of blocked IP addresses)
- Verify if the geographical location of the IP address matches an allowed city wall location.
- Verify if the geographical location of the IP address is blocked by the application.
If the incoming user's IP address does not match any of the above rules, the incoming request will be accepted.
Have a question? You can always send us an email at support@unloq.io, or contact us on chat.
For security related concerns, please visit our Security page.